1. I get a lot of queries on my blog posts related to cyber security courses and any time I am in some forum or discussion from all range age groups regarding serious career scope in India in the field of Cyber Security.Is it worth taking a plunge in a field which currently only has more of a keen interest value rather then offering lucrative pay packet job?The younger age group which generally has young engineering graduates look little restless of taking the risk but the field is pretty exciting for those who are passionately interested in it.
2. The field is immense and huge to start with.For a fresher it would be pretty cumbersome to find where to start from.The moment any typical search is made for a cyber security course on google,the results are too huge and confusing to get started on.For a novice guy who doesn’t have any background in this field but keen to start a career in this field, I would submit few first steps to start before ways and career road automatically starts guiding ahead.
3. Firstly,make it very clear in your mind that this field is very dynamic...you have to be continuously on your toes to be updated around what’s happening in this field.Millions of cyber incidents are happening,thousands of zero days are being discovered,thousands of case studies are being released about various cyber incidents and as you start understanding you need to prioritize of what all to grasp in detail .....follow up good tweets of cyber security experts.The courses you do in this field will not be like the typical graduation certification that you do once and will make you a B.Tech for the rest of your life without ever some one asking about the syllaabi.Most of the course and certification have a shelf life of 2-3 years after which you need to renew them to continue your professional standing in the market.
4. The best thing about this field is that you can build your career and get your basics clear by putting in you hard-work along with the world of open-source that’s your window to knowledge bank.Be it the white papers or applications or Operating systems etc most of the entire gambit of tools is free....yes...for last about 8-9 years of my association with the field I have not bought or purchased any software or OS or toolkit to practice basic hacks and penetration tests.
5. For a start in respect of courses....I would submit that most of the courses valued globally like CEH,CISSP etc by EC-COUNCIL are pretty costly and just doing them does not guarantee anything with respect to job.You have to be aware of lots besides these courses.For a start for a typical Indian novice fresher I would recommend to start with CCCSP,CCCS etc...links given below :
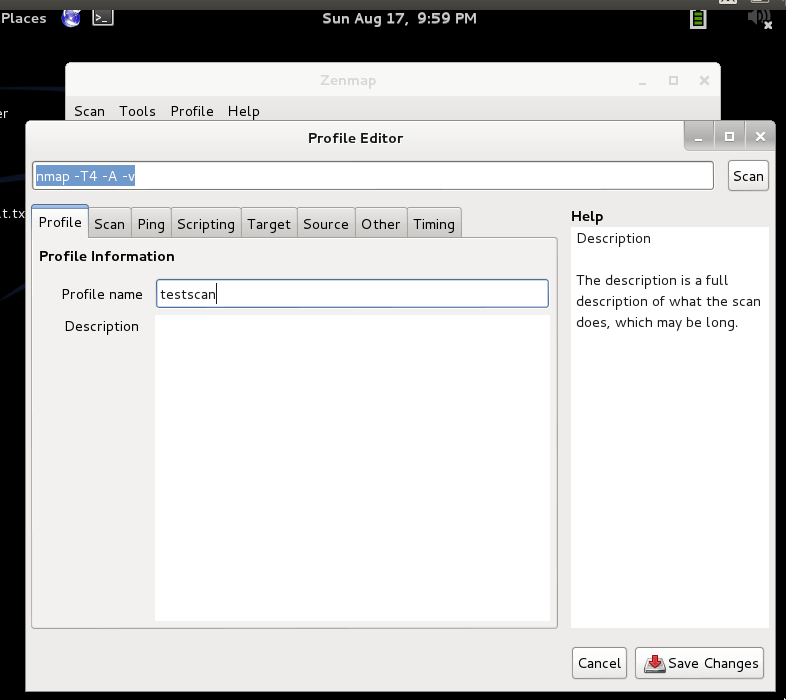
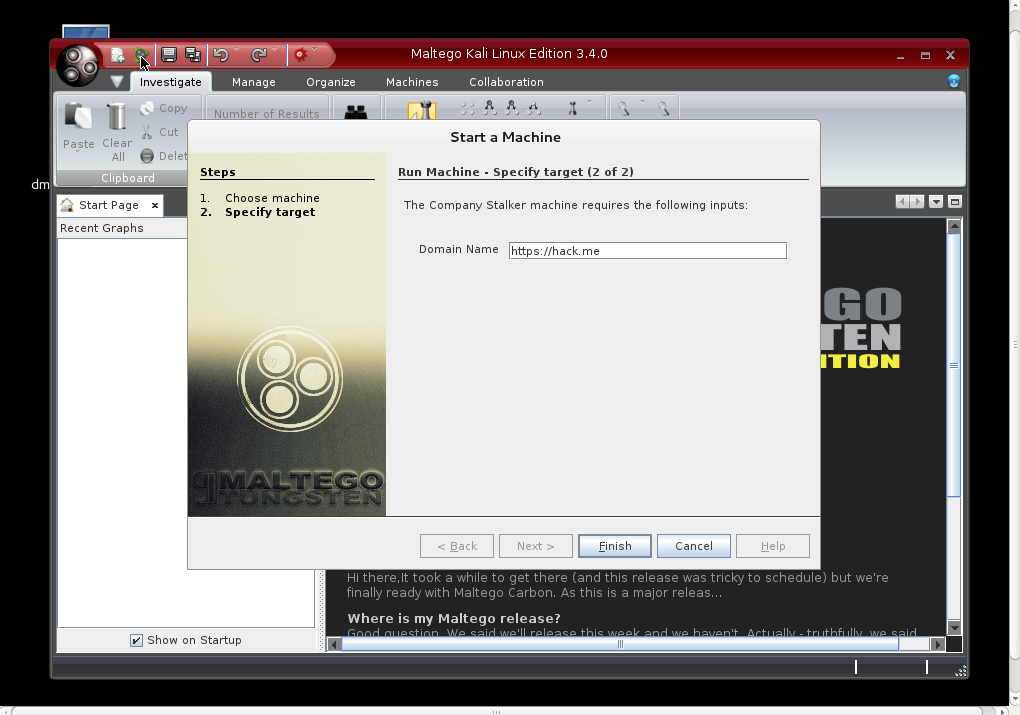
6. Besides these courses which only give a very basic over view of the field,you should start getting conversant with LINUX flavors available viz UBUNTU, Fedora, OpenSuse, Linux MInt etc to mention a few....besides a horde of excellent security distros are available with all possible youtube videos and manuals on the net for helping from scratch.Get conversant and start playing with maximum tools available in these.Few of the distros that I would recommend are listed below :
- Kali Linux at
- BackBox at
- BackTrack R3 at
- Knoppix STD
- Pentoo
- DEFT
- Parrot
- Caine
- Samurai Web Testing framework
- Matriux Krypton
- Bugtraq
- Node zero
- Cyb org
- Helix
- Network SEcurity Toolkit
- Wireshark(not an OS)
- GRML
- Chaos
- Katana
- Damn Vulnerable Linux
- Auditor
and I must tell you these are only few to test before you start getting basic idea of what’s happening around.
7. You have to be passionate enough to carry yourself successfully in this field.The moment you are out of touch for whatever reasons you have a lot to catch.Every thing is available on the net..be it the study material...be it any software to start.....you actually do not straight away enrol for a course..prepare yourself with the basics as available vide these distros...basic linux and then do some course to start building your documented profile.If you have reached reading here and you have queries you can get back to me here ....post a comment.
 https://orcid.org/0000-0002-9097-2246
https://orcid.org/0000-0002-9097-2246