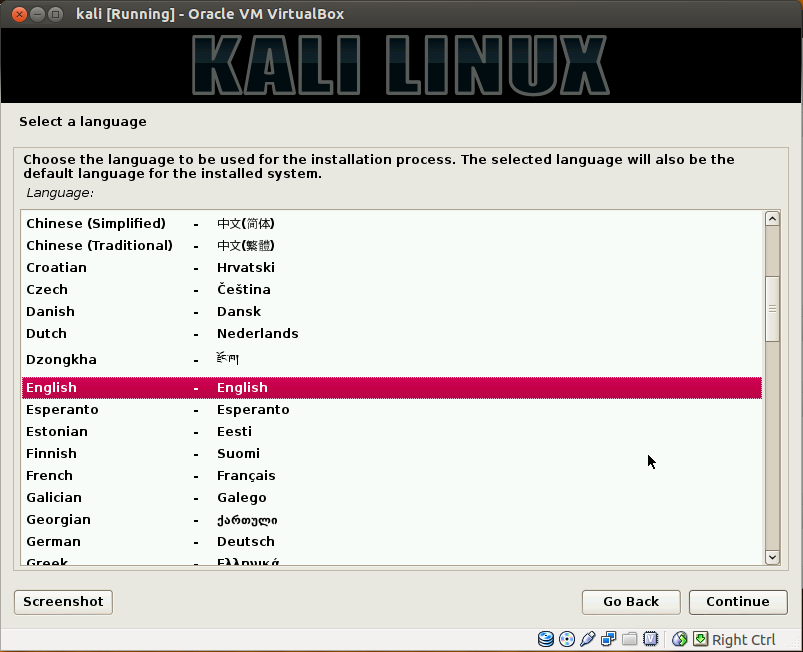
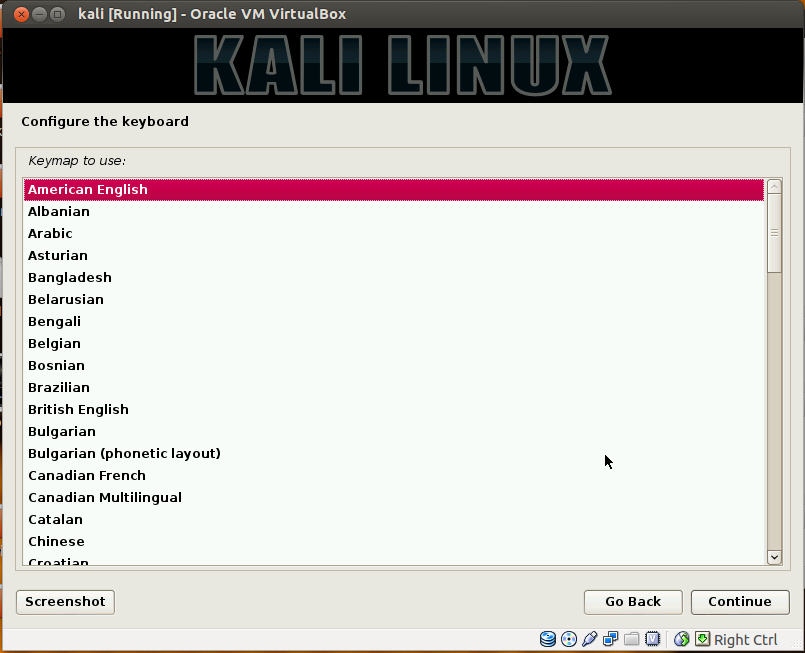
Kali Linux is a Debian-derived Linux distribution designed for digital forensics and penetration testing. It is maintained and funded by Offensive Security Ltd. It was developed by Mati Aharoni and Devon Kearns of Offensive Security through the rewrite of BackTrack, their previous forensics Linux distribution.Kali Linux is preinstalled with numerous penetration-testing programs, including nmap (a port scanner), Wireshark (a packet analyzer), John the Ripper (a password cracker), and Aircrack-ng (a software suite for penetration-testing wireless LANs). Kali Linux can be run from a hard disk, live CD, or live USB. It is a supported platform of the Metasploit Project's Metasploit Framework, a tool for developing and executing security exploits.This post brings you the screen step wise shots during installation....
Showing posts with label backtrack 5. Show all posts
Showing posts with label backtrack 5. Show all posts
Wednesday, July 16, 2014
Saturday, November 23, 2013
BACKTRACK 5 R3 : 0trace
This post is going to introduce you to a "Identify Live Hosts" tool by the name of 0trace that enables a user to perform hop enumeration (“traceroute”) within an established TCP connection, such as a HTTP or SMTP session. This is opposed to sending stray packets, as traceroute-type tools usually do. The important benefit of using an established connection and matching TCP packets to send a TTL-based probe is that such traffic is happily allowed through by many stateful firewalls and other defenses without further inspection (since it is related to an entry in the connection table).
How to reach 0trace ?
The command syntax :
root@bt:/pentest/enumeration/0trace# ./0trace.sh eth0 (IP ADDRESS1)
and then you need to then open another terminal and connect using netcat as below
root@bt:~# nc (IP ADDRESS1) 80
Here in the example as shown vide screenshots,i have used a web site ip address for sample check....without opening the second terminal window...you will not get any progress on the first terminal....
How to reach 0trace ?
 | |
| (Click to enlarge) |
 |
| (Click to enlarge) |
 |
| (Click to enlarge) |
root@bt:/pentest/enumeration/0trace# ./0trace.sh eth0 (IP ADDRESS1)
and then you need to then open another terminal and connect using netcat as below
root@bt:~# nc (IP ADDRESS1) 80
Here in the example as shown vide screenshots,i have used a web site ip address for sample check....without opening the second terminal window...you will not get any progress on the first terminal....
Sunday, September 29, 2013
BACKTRACK 5 R3 : dnsrecon
1. Dnsrecon is another nice easy to use tool for pen testers for enumeration. The kinds of things dnsrecon can do are as follows:
- Reverse Lookup against IP range
- Perform general DNS query for NS,SOA and MX records
- Cache snooping against Name Servers
- Google Scanning for Sub Domains and Host
2. The command line usage and the few imp switch execution details are briefed here down :
-h --help Show this help message and exit
-d --domain Domain to Target for enumeration.
-c --cidr CIDR for reverse look-up brute force (range/bitmask).
-r --range IP Range for reverse look-up brute force
-n --name_server Domain server to use, if none is given the SOA of the
target will be used
-D --dictionary Dictionary file of sub-domain and hostnames to use for
brute force.
-t --type Specify the type of enumeration to perform:
Available through :
Backtrack -> Information Gathering -> Network Analysis -> DNS Analysis -> dnsrecon
In this blog post,I will be covering 3 enumeration techniques. These being:
SRV records Enumeration
Top Level Enumeration
Standard Enumeration
To perform an SRV records enumeration against a domain the following input command will be run:
Code:
./dnsrecon.py -t srv -d
As an example if we wanted to do this to certifiedhacker.com, our command would be as follows:
Code:
./dnsrecon.py -t srv -d google.com
Code:
./dnsrecon.py -t std -d
Using Google as an example again, our command would be:
Code:
./dnsrecon.py -t std -d google.com
- Reverse Lookup against IP range
- Perform general DNS query for NS,SOA and MX records
- Cache snooping against Name Servers
- Google Scanning for Sub Domains and Host
2. The command line usage and the few imp switch execution details are briefed here down :
-h --help Show this help message and exit
-d --domain Domain to Target for enumeration.
-c --cidr CIDR for reverse look-up brute force (range/bitmask).
-r --range IP Range for reverse look-up brute force
-n --name_server Domain server to use, if none is given the SOA of the
target will be used
-D --dictionary Dictionary file of sub-domain and hostnames to use for
brute force.
-t --type Specify the type of enumeration to perform:
Available through :
Backtrack -> Information Gathering -> Network Analysis -> DNS Analysis -> dnsrecon
In this blog post,I will be covering 3 enumeration techniques. These being:
SRV records Enumeration
Top Level Enumeration
Standard Enumeration
 | ||
| (Click on image to Enlarge) |
 | ||
| (Click on image to Enlarge) |
Code:
./dnsrecon.py -t srv -d
As an example if we wanted to do this to certifiedhacker.com, our command would be as follows:
Code:
./dnsrecon.py -t srv -d google.com
 |
| (Click on image to Enlarge) |
Top Level Enumeration
For performing a top level enumeration the following command will be used :
Code:
./dnsrecon.py -t tld -d
If the same command is run for google.com,the following command will be used
Code:
./dnsrecon.py -t tld -d google.com
For performing a top level enumeration the following command will be used :
Code:
./dnsrecon.py -t tld -d
If the same command is run for google.com,the following command will be used
Code:
./dnsrecon.py -t tld -d google.com
 |
| (Click on image to Enlarge) |
 |
| (Click on image to Enlarge) |
and similarly,to perform an STD (standard) enumeration,the following command is used :
Code:
./dnsrecon.py -t std -d
Using Google as an example again, our command would be:
Code:
./dnsrecon.py -t std -d google.com
The result as seen below in a standard enumeration :
 |
| (Click on image to Enlarge) |
 |
| (Click on image to Enlarge) |
Labels:
backtrack 5,
backtrack 5 R3,
cccsp,
CEH,
certified ethical hacker,
DNSDICT6,
dnsmap,
dnsrecon,
Hack Tools,
hacking,
Hacking Class,
Information Gathering,
IP address,
ipv6,
Know Your Backtrack,
Linux,
Tutorial,
ubuntu
BACKTRACK 5 R3 : dnsmap
1. Another useful tool for information gathering is dnsmap....few of you guys may wonder of why to use a variety of tools for information gathering when most of them give more or less the same result.The answer lies in the fact that any kind of additional information can be a hole to exploit later...so in the stage of information gathering,it is always better to collect as much info as possible...so few quickies about what is the purpose of this tool...
- Get IP addresses associated to each successfully bruteforced subdomain, rather than just one IP address per subdomain.
- Bypassing of signature-based dnsmap detection by generating a proper pseudo-random subdomain when checking for wildcards.
- Abort the bruteforcing process in case the target domain uses wildcards.
- Ability to be able to run the tool without providing a wordlist by using a built-in list of keywords.
- Saving the results in human-readable and CSV format for easy processing.
- Improved built-in subdomains wordlist.
- New bash script (dnsmap-bulk.sh) included which allows running dnsmap against a list of domains from a user-supplied file. i.e.: bruteforcing several domains in a bulk fashion.
[ Source : http://stylodj.wordpress.com/category/how-to-use-dnsmap-tool-backtrack-5-rx/]
2. So to get to this tool...we need to follow the same route as we have been doing it in past...vide the information gathering sub menu as shown below :
Backtrack - Information Gathering - Network Analysis - DNS Analysis - dnsmap
 | ||
| (Click on the image to enlarge) |
3. The basic syntax and switches for the tool are :
./dnsmap sitename.com [options]
and the switches are :
- w for wordlist file)
- r for regular results file
- c for csv results file
- d for delay millisec
- i for ip's to ignore
4. The screens below show the usage and execution part as it happens on the screen.
 |
| (Click on the image to enlarge) |
 |
| (Click on the image to enlarge) |
 |
| (Click on the image to enlarge) |
5. What we are attempting vide the command executed is to bruteforce all of the subdomains of certifiedhacker.com and saving them to a file called result. I have truncated the output since its very long and thus avoided.So I have only shown some part from the beginning and then as it ends.IN addition if one has a custom wordlist of subdomains he/she can use that as well simply by specifying the -w argument and then the path to the wordlist.So after the run is executed,the final results are seen in a manner shown below vide the screenshots :
 |
| (Click on the image to enlarge) |
So as seen in the results above...we see there are 924 subdomains with their respective IP addresses.Though in the screen shots above,we see a common IP address since it is a site for CEH testers.
 |
| (Click on the image to enlarge) |
 |
| (Click on the image to enlarge) |
In the screen shots above,the result file created is seen and read...so u can see the kind of contents that are stored in the file so generated....
Labels:
backtrack 5,
backtrack 5 R3,
cccsp,
CEH,
certified ethical hacker,
DNSDICT6,
dnsmap,
Hack Tools,
hacking,
Hacking Class,
Information Gathering,
IP address,
ipv6,
Know Your Backtrack,
Linux,
Tutorial,
ubuntu
Saturday, September 28, 2013
BACKTRACK 5 R3 : dnsenum
1. Coming to next good information gathering tool in Backtrack 5 R3...here I give the command run details and a sample result by a tool known as dnsenum
First a small Intro about the tool :
DNSenum is a tool that is designed with the purpose of enumerating DNS information about a domain.Then information that one obtain's from this tool is useful for the phase of information gathering when one is conducting a penetration test.Thus the basic purpose of Dnsenum is to gather as much information as possible about a domain. The program performs the following operations:
- Get the host's addresse (A record)
- Get the nameservers (threaded)
- Get the MX record (threaded)
- Perform axfr (ie DNS zone transfer) queries on nameservers
- Get extra names and subdomains via google scraping (google query = "allinurl: -www site:domain")
- Brute force subdomains from file, can also perform recursion on subdomain that have NS records (all threaded)
- Calculate C class domain network ranges and perform whois queries on them (threaded)
- Perform reverse lookups on netranges ( C class or/and whois netranges) (threaded)
- Write to domain_ips.txt file ip-blocks
- Get the host's addresse (A record)
- Get the nameservers (threaded)
- Get the MX record (threaded)
- Perform axfr (ie DNS zone transfer) queries on nameservers
- Get extra names and subdomains via google scraping (google query = "allinurl: -www site:domain")
- Brute force subdomains from file, can also perform recursion on subdomain that have NS records (all threaded)
- Calculate C class domain network ranges and perform whois queries on them (threaded)
- Perform reverse lookups on netranges ( C class or/and whois netranges) (threaded)
- Write to domain_ips.txt file ip-blocks
 |
| (Click on the image to enlarge) |
Backtrack - Information Gathering - Network Analysis - DNS Analysis - dnsenum
you get to see the following screen...
 |
| (Click on the image to enlarge) |
./dnsenum.pl sitename.com
 |
| (Click on the image to enlarge) |
 |
| (Click on the image to enlarge) |
BACKTRACK 5 R3 : DNSDICT6
1. I have been using and playing with BT5 R3 for quiet some time now...and having used and practised about 50% of them...I have decided to start sharing and how to use them on my blog for the firstimers..with screen shots and screen cast when required....although I have shown few tools and exploits of BT5 earlier .... now I wish to just make it all systematic....and in the first attempt here I am giving out a step by step screen shot of how to use the tool DNSDICT6...
2. The route to dnsdict6 is show in the screen shot below :
Backtrack - Information Gathering - Network Analysis - DNS Analysis - dnsdict6
3. As can be made out from the Backtrack menu drop down...since it is listed in the information gathering sub menu..it is a Information Gathering tool. This tool is used to find all the sub-domains of a website or web server. The most advanced use of DSNDICT6 is to enumerate all IPv4 and IPv6 addresses and extract the dumps like sub-domains, IP information. This tool is quite a powerful tool because it also extracts those sub domains which are restricted or invisible for users.With respect to the usage and screens...they are seen below :
 |
| (Click on the image to Enlarge) |
Once you click this dnsdict6...u get the following screen :
 |
| (Click on the image to Enlarge) |
Before we execute the command,let us see the command syntax & switches available :
The switches details are seen below :
- d is used to display information on Name Servers and MX Records
- 4 is used to dump IPv4 addresses.
Four types of dictionary are inbuilt in this tool as follows :
- s (mall=50),
- m (edium=796) (DEFAULT)
- l (arge=1416), and
- x (treme=3211).
- t is used to specify no. of threads.
- t is used to specify no. of threads.
MX record ie mail exchanger record is a type of resource record in the
Domain Name System that specifies a mail server responsible for
accepting email messages on behalf of a recipient's domain, and a
preference value used to prioritize mail delivery if multiple mail
servers are available. The set of MX records of a domain name specifies
how email should be routed with the Simple Mail Transfer Protocol
(SMTP).
So for example we run this command on http://certifiedhacker.com/
 |
| (Click on the image to Enlarge) |
The command reads :
dnsdict6 -d46 -s -t 10 certifiedhacker.com
 |
| (Click on the image to Enlarge) |
In the command above I have used the small dictionary with 10 threads to minimize the running time...so actually this is a limited result...would have been slightly different had the same been run with xtreme dict and large number of threads...
Subscribe to:
Posts (Atom)
 https://orcid.org/0000-0002-9097-2246
https://orcid.org/0000-0002-9097-2246