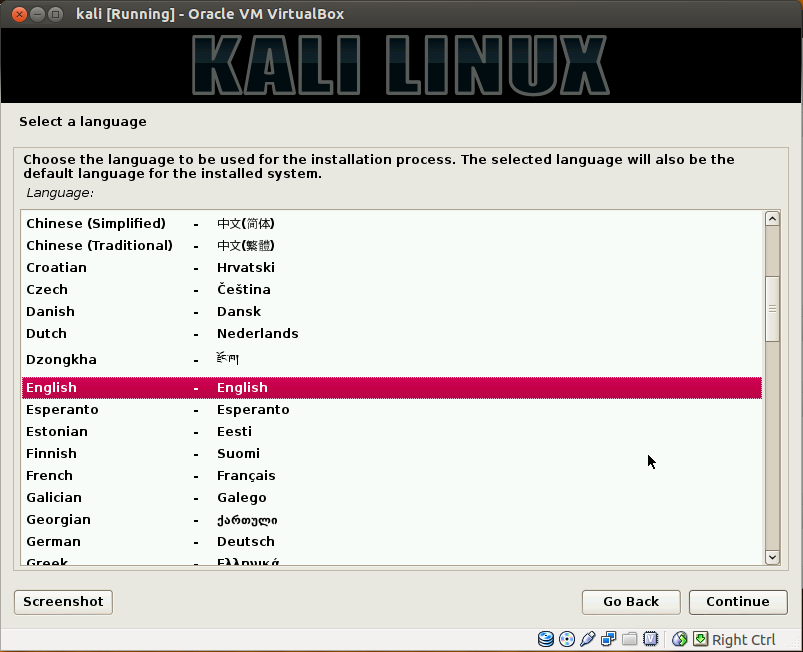
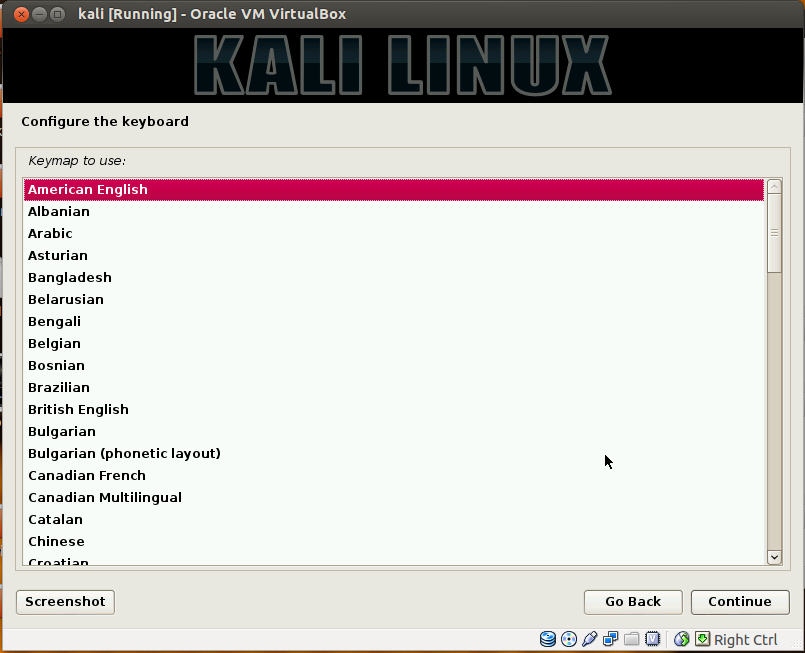
Kali Linux is a Debian-derived Linux distribution designed for digital forensics and penetration testing. It is maintained and funded by Offensive Security Ltd. It was developed by Mati Aharoni and Devon Kearns of Offensive Security through the rewrite of BackTrack, their previous forensics Linux distribution.Kali Linux is preinstalled with numerous penetration-testing programs, including nmap (a port scanner), Wireshark (a packet analyzer), John the Ripper (a password cracker), and Aircrack-ng (a software suite for penetration-testing wireless LANs). Kali Linux can be run from a hard disk, live CD, or live USB. It is a supported platform of the Metasploit Project's Metasploit Framework, a tool for developing and executing security exploits.This post brings you the screen step wise shots during installation....
Showing posts with label wireshark. Show all posts
Showing posts with label wireshark. Show all posts
Wednesday, July 16, 2014
Saturday, August 03, 2013
Is PORT SCANNING legal in INDIA?
1. The IT security guys have so much to experiment and learn vide unending open source information and tools available on the net.Be it BACKTRACK or Wireshark or Nmap or nessus or Canvas(not opensource) or a web scanner like Acunetix or Arachini and the list is unending....there is lots to do...but do we actually know that simply running a port scan on the internet is a crime in other parts of the world?
2. In countries like Australia,UK , port scanning is recognized as a "potential attempt" to infringe on a system and that's a simple truth....no body would run such tools openly available without intent. Yess!!!...the intent can be educating self but the other side can be bad intent and no one can prove whats the intent inside the person's mind.It may change the moment he realizes he/she is caught.In the United States there is no need to prove intent and port scanning is considered illegal.So even installation of such tools is a crime.So if a naive script kiddie from India goes with his laptop to US with a virtual box machine holding a OS with a port scanner...he is a cyber criminal the moment he lands in the US.
3. Today we in India do not have straight and clear laws defining whether running such tools or installation is a crime or not coz the whole thing is COMPLEX.The compliance laws across countries vary and that too drastically...it may be acceptable in a country like India and it may be serious offence in US.So seeing from the current state of affairs in India,it does not look like if a day will be near when such stringent guidelines exist in India to restrict all these uses and installations...or let it be restricted to professionals only.....but then who will define a Cyber Security Professional....CDAC or CEH or some other such agency....these institutes can be a critical node in identifying and certifying cyber security professionals to measure and endorse the intent...but at the end of the day we all are humans...and we know that "too err is human"....so a agency certified person finally has himself to decide whether he uses a black hat or a white hat!!!! :-)
4. Meanwhile students and IT security enthusiasts should take care of running such tools on the internet coz these are serious tools who can break into some one's privacy...and if the victim gets serious after you...things will be bad enough to land you behind bars...so the best place to experiment with such tools is a virtual environment that can be available vide Virtual box or vmware etc....Security guys and enthus should be familiar with the excellent Open Source Security Testing Methodology Manual (OSSTMM), which provides best practices for these situations.
PLEASE TAKE CARE TO RUN THE CYBER SECURITY TOOLS BEFORE THE LAW STARTS RUNNING AFTER YOU
Labels:
backtrack,
canvas,
cccsp,
CDAC,
CDAC Certified Cyber Security Professional,
CEH,
cissp,
cyber law,
cyber security,
CYBER SECURITY COURSE,
legal issues,
malicious,
nessus,
nmap,
OPENSOURCE,
OSSTMM,
wireshark
Saturday, December 22, 2012
MALWARE via SUDOKU via EXCEL SHEET
1. Sudoku is good for you brain....but it may compromise your PC if you have downloaded one of the excel files with embedded malicious script inside that offers you to play the subject game. Peter Szabo from SophosLabs has identified a piece of malware that resides behind a Microsoft Excel-based Sudoku generator. The Malware developed in Visual Basic requires macros, a scripting language that allows users to create equations based on values in different columns and rows. Microsoft – Malware behind Microsoft Excel-based Sudoku generator.
 |
| CLICK TO ENLARGE |
2. Although by default the macros are disabled in any Microsoft Office application....but any one who downloads the excel file would eventually enable the macros that run the script to play the game...so he can keep playing the game while the script in the background sets up the malware and establishes contact with its master bot.....so like always the updated Antivirus on the system will keep sitting without catching up anything.....so comes the importance of packet analyzers like Wireshark....ethreal etc...but then it becomes slight technical which in most cases would be out of purview for a common user.
Saturday, October 22, 2011
WIRESHARK Troubleshoot
1. The most common trouble that comes up first time users of Wireshark is that CAPTURE INTERFACE drop down shows the NPF not running and thus the interface list shows NIL.....
Subscribe to:
Posts (Atom)
 https://orcid.org/0000-0002-9097-2246
https://orcid.org/0000-0002-9097-2246