1. Most of us would have heard of the pretty famous Nmap ("Network Mapper") ,a free and open source (license) utility for network discovery and security auditing.It uses raw IP packets in novel ways to determine what hosts are available on the network, what services those hosts are offering, what operating systems they are running, what type of packet filters/firewalls are in use, and dozens of other characteristics. Designed to rapidly scan large networks Nmap runs on all major computer operating systems.Official binary packages are available for Linux, Windows, and Mac OS X. In addition to the classic command-line Nmap executable, the Nmap suite includes an advanced GUI and results viewer (Zenmap), a flexible data transfer, redirection, and debugging tool (Ncat), a utility for comparing scan results (Ndiff), and a packet generation and response analysis tool (Nping).In this post the focus will be to introduce Zenmap...a kind of GUI for running NMAP commands which is otherwise terminal based.
2. To open Zenmap, go to the Backtrack menu. Navigate to Information Mapping - DNS Analysis, and click Zenmap.
3. Notice that under the Profile menu that there are several options to determine what type of scan you would like to run, as shown in the following screenshot:
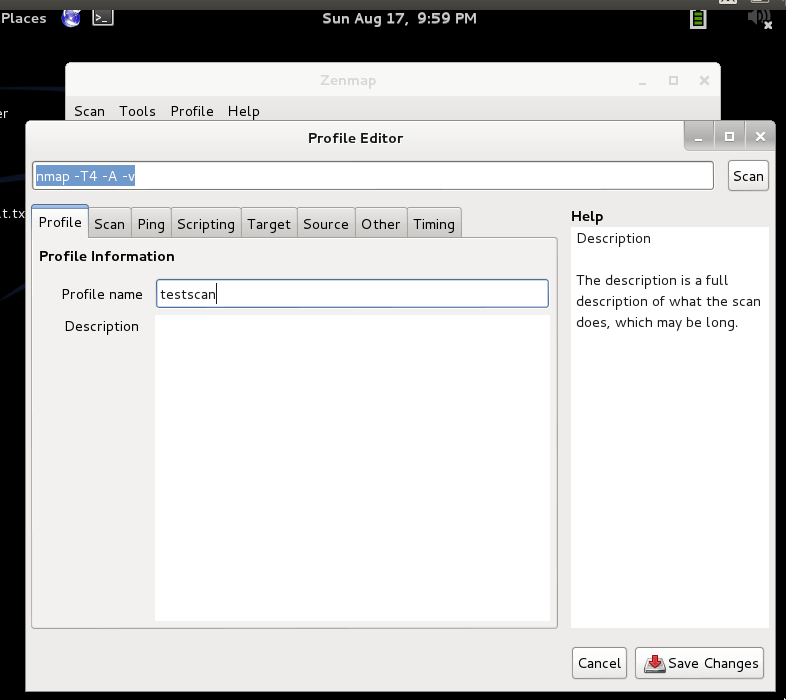
4. The first step is creating a new profile. A profile in Zenmap allows a Penetration Tester to create what type of scan to execute and what different options to include.Navigate to the Profile menu and select New Profile as shown in the following screenshot:
5. When you select New Profile, the profile editor will launch. You will need to give your profile a descriptive name. For example, you can call the profile testscan as I have named here.Optionally, you can give the profile a description. During your course of using Zenmap you will probably create many profiles and make multiple scans.
6. Zenmap is the best way to get output from Nmap scans. Zenmap offers a rich graphical user interface that displays scans that can be exported into different formats, such as text or Microsoft Excel.
3. Notice that under the Profile menu that there are several options to determine what type of scan you would like to run, as shown in the following screenshot:
4. The first step is creating a new profile. A profile in Zenmap allows a Penetration Tester to create what type of scan to execute and what different options to include.Navigate to the Profile menu and select New Profile as shown in the following screenshot:
5. When you select New Profile, the profile editor will launch. You will need to give your profile a descriptive name. For example, you can call the profile testscan as I have named here.Optionally, you can give the profile a description. During your course of using Zenmap you will probably create many profiles and make multiple scans.
6. Zenmap is the best way to get output from Nmap scans. Zenmap offers a rich graphical user interface that displays scans that can be exported into different formats, such as text or Microsoft Excel.
 https://orcid.org/0000-0002-9097-2246
https://orcid.org/0000-0002-9097-2246