1. Privacy International , a UK-based registered charity that defends and promotes the right to privacy across the world, lost a case challenging RIGHT TO PRIVACY.
So as it stands the GCHQ now has a official tick to itself forcing into hacking devices to obtain intelligence thereby ensuring National Security interests.The court ruled in favor of GCHQ and thus for the first time the GCHQ has confirmed that it has been associated with hacking into IT and computer devices which till date were only thought in anticipation or were believed right based on the NSA whistle blower Edward Snowden.
Source : http://www.wired.co.uk/news/archive/2015-03/20/gchq-hacking-faq
Source : http://www.wired.co.uk/news/archive/2015-03/20/gchq-hacking-faq
2. An extract produced as follows from http://www.bbc.com/news/uk-politics-35558349
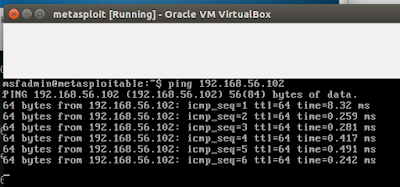
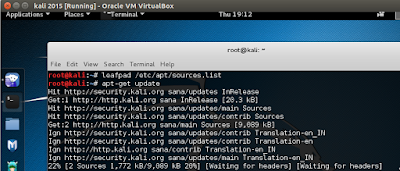
"Hackers can remotely activate cameras and microphones on devices,
without the owner's knowledge, log keystrokes, install malware, copy
documents and track locations among other things"
3. Another extract produced below from the Investigatory Powers Tribunal (IPT) complete copy of which is available for reading at http://www.ipt-uk.com/docs/Privacy_Greennet_and_Sec_of_State%20.pdf reads as follows :
"The use of computer network exploitation by GCHQ, now avowed, has obviously raised a number of serious questions, which we have done our best to resolve in this Judgment. Plainly it again emphasises the requirement for a balance to be drawn between the urgent need of the Intelligence Agencies to safeguard the public and the protection of an individual's privacy and/or freedom of expression."
3. How much of this stands right or wrong irrespective,but one thing has come out large and clear....there stands no privacy while anyone is on the net...whatever you may do or attempt from your mobile device or the computer,nothing is yours.....
 https://orcid.org/0000-0002-9097-2246
https://orcid.org/0000-0002-9097-2246