1. Strange it may seem but the current availability of Laptops for sale in the market show a peculiar sad state of specs...ie they are available only with Windows 8.There are rare options on few sites that offer New laptops for sale without Windows OS.I have been planning to buy a laptop with i3/i5 processor and in my search over various sites I came across this sad but surprising stat.
2. Infact leading online shopping retails in Dubai have got NIL option to buy a laptop without Windows 8.I checked up at the following sites :
- http://www.carrefouruae.com/
- http://www.ic4uae.com/
3. Even the options without Windows 8 on leading retails in India have much lesser options then with Windows 8. Checked up at Flipkart, snapdeal,timesofindia shopping to mention a few.
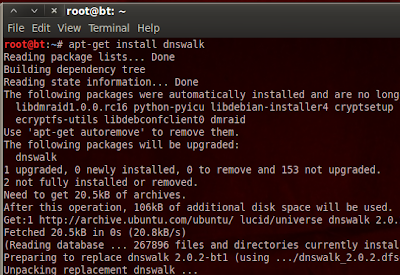
4. Given these facts...it looks like Microsoft has put in rigorous and vigorous marketing efforts to increase there sales graph for Windows 8.For those guys who wish to buy Windows 8 laptop and then attempt removing the windows and install some Linux flavour...it is equally surprising that unlike till Windows 7 wherein it was relatively a matter of deleting Windows and installing Linux...it is complex removing Windows 8 so the user has to be content with a dual boot option wherein he has to compromise with wastage of space dedicated to Windows....
5. Thus there is a kind of binding that comes along with these laptops with Windows 8 that you cannot mov to another OS.....:-(
 https://orcid.org/0000-0002-9097-2246
https://orcid.org/0000-0002-9097-2246