1. Each Antivirus software in the web market today claims as the First and the topmost rated antivirus amongst all.Each has a claim that says "We check what others don't".A large percentage of typical user have actually got no way to check out who is the actual one...Who is the BEST? They then generally select the one that is based on the recommendations of their social circle and the convincing factor generated by the site of the product or simply put...it can ba random selection at last. In fact in my quest to search the best one amongst all....the number of QRs that one needs to check for one antivirus is a long one.Few of the qualities that should not be missed at all are briefly enumerated below.
WEST COAST LABS ANTI-VIRUS : The West Coast Labs Checkmark certification for antivirus effectiveness. WCL stands as a global leader in research, testing and certification for information security products and services. They have market-leading technology and testing facility in the UK, USA and india.Their services are being used by the leading global brands to create market advantage and by large business enterprises for obtaining crucial technical insight into product performance.WCL provides an authoritative and independent service, delivering sound, meaningful technical information on which critical business decisions can be made.More at http://www.westcoastlabs.org/
ICSA CERTIFIED : The ICSA is an independent organization that has a set criteria for certifying antivirus software.
AV COMPARATIVES : Anti-Virus Comparative test conducted in 2010. Overall scores are presented as Advanced + (A+), Advanced (A), Standard, and Tested.
SCOPE OF PROTECTION : Does the product protect from every threat? This rating evaluates the breadth and depth of security from the software. While most security solutions tout “multi-layered” protection, “360 degree” defense and/or even “100%” security, some are certainly more thorough than others. The best antivirus solutions will include traditional protection from viruses, worms, Trojans and spyware, but should also include defense from keyloggers, phishing scams, email-borne threats and rootkits. While antivirus programs are by no means full-blown internet security suites, they should protect from as many threats on as many fronts as they can.
EFFECTIVENESS : How effective is the application at protecting your computer from harmful viruses and other malware? This rating combines various tests and certifications to determine how well the software performs. Antivirus is specifically designed to protect your computer, so if it doesn’t do that well, what good is it? All the features, bells and whistles, or sleek interface can’t make up for poor performance. We look at results from the industry-standard security software testers and professional security organizations to find the most effective software available and evaluate overall effectiveness. In general, our highest ranked programs are also the most effective.
HACKERS : Anyone trying to take control of your computer for malicious purposes.
PHISHING : These criminal scams attempt to obtain your identifying information by disguising as legitmate sources (like your bank, eBay, or facebook).
ACTIVEX : Several Microsoft programs use ActiveX controls for good, but these components can also be taken advantage of.
USER PROFILES : The software includes distinctive interfaces or features for particular users (often beginners or advanced users).
SELF-DEFENSE : The software monitors itself and the computer, effectively protecting from intrusions or unauthorized changes.
SCHEDULING : The ability to schedule specific scans to occur at a specific time or interval.
HISTORY/REPORT LOGGING : The software keeps a record of the performed tasks and results for future reference or reporting.
SILENT / GAMER MODE : The 'gamer' mode allows you to use the computer in full-screen mode (for games, presentations, or videos) without interruptions from the security software.
LAPTOP / BATTERY SAVING MODE : The software can be set to delay scans or intensive processes for later in order to increase battery life.
LINK SCANNER : An integrated web tool that monitors web links and prevents/warns users from clicking on malicious sites.
BOOTABLE RESCUE CD :In the event of a complete system crash, you can use the bootable rescue disc to preempt the OS and clean the system.
FREE VIRUS SCAN ONLINE : The security manufacturer offers a free virus scan online (often with incentive to purchase their products for removal capabilities).
AUTOMATIC DEFINITION UPDATES : The program automatically updates virus definitions or DAT files. A virus definition is basically the formula that the software uses to determine if a file is infected by a specific virus.
MANUAL DEFINITION UPDATES : You can manually check for virus definition updates.
SCHEDULED UPDATES : Updates can be scheduled to run at a specific time or interval.
PULSE/PUSH UPDATES : Small, regular updates are initiated by the manufacturer as needed to deliver important updates.
ROLLBACK : The ability to revert to a previously working state if the most recent update causes a problem.
MANUAL SCANNING : Manual Scanning is the ability to start a scan of your hard drive at any time.
QUICK & DEEP SCAN : Manual and/or scheduled scans can either be quick (scan most important areas) or deep (full scan of computer).
OPTIMIZED SCANNING : The software is configured to scan efficiently, only scanning areas and files that have changed since the last scan.
SCAN INDIVIDUAL FILE(S) : The software can scan an individual file for viruses. This is often available by right-clicking on the file and choosing to scan.
EXCLUDE FILES : The software allows the user to designate certain files, folders, or drives NOT to include in the virus scan.
SCAN COMPRESSED FILES : Scans zipped (.zip) or other compressed files that are usually obtained through emails or downloaded from the web.
QUARANTINES INFECTED FILES : If a file is suspected of being infected with a virus, it moves the file to a "quarantine" area where you cannot accidentally access it.
AUTO-CLEAN INFECTED FILES : The anti-virus program will automatically clean or fix files that are infected.
SCAN USB (AND OTHER EXTERNAL DRIVES) : The software is capable of scanning external drives for viruses.
PASSWORD PROTECT SETTINGS : Prevents the Anti-Virus settings from being modified by other users.
ADJUSTABLE SECURITY LEVELS : Security can be customized and set to a particular level of potency.
VULNERABILITIES : Microsoft and third-part software vendors are constantly providing security patches or other updates. Some software takes a proactive approach and helps you stay on top of the most recent updates.
COOKIES : Though not typically malicious, cookies are little chunks of code stored on your computer from web sites.
SCRIPTS : Script Blocking technology monitors Java and VBS scripts and alerts users of virus-like behavior. They stop these viruses before they can infect a system without needing virus definitions.
SPAM : Spam is unwanted email, whether it's annoying advertisements or a link to a virus.
AUTO USB DETECT : Most antivirus software can scan USB drives, but some automatically detect when an external drive is plugged in and will block malware from automatically running.
VIRUS SIGNATURES: Traditional virus detection is based on identifying malware by matching it with known viruses.
BLACKLISTING : Setting a file or website on the "blacklist" means that it should never be allowed.
WHITELISTING : Setting a file or website on the "whitelist" means that you trust it and don't need the security software to scan/block it.
HEURISTICS : Proactive virus blocking is possible with behavioral analysis, file emulation, and/or generic signature detection.
REAL-TIME : Real-time protection means that the software protects you from viruses automatically, while the data is being accessed.
SECURITY NETWORK : This security approach involves the software manufacturer gathering anonymous information about your system in order to benefit everyone. If a virus is found on your computer, they can quickly find the cause and update definitions for all users.
ON-ACCESS SCANNING : Your files are scanned when you receive them and when you try to access them.
ON-DEMAND SCANNING : You can determine which files and when to scan for viruses. It's like manual scanning but you can be more specific and scan a file at a particular time. Simply right-click on the filename.
ADWARE : Though not always harmful, these annoying programs cause advertisements to display on your computer without your permission.
EASE OF INSTALLATION : How easy is the product to download, install, and setup? This rating is determined by install speed and simplicity. Security software shouldn’t be a chore to install, and should have you protected as soon as possible. From download to install, to the first scan; implementing antivirus software should be quick and easy.
EASE OF USE : How usable is the product? The Ease of Use rating reflects how easy the product is to use, run, and maintain. Antivirus software is complex stuff, but shouldn’t require a degree in computer security. The best security programs have all the features security experts want, but are just as easily used by a beginner. Everyday computer users want a security solution that they can install and forget about; software that doesn’t require constant maintenance or have annoying interruptions. The best antivirus software is flexible enough to do exactly what you want to (even if that means running by itself).
FEATURES : Does the software include additional benefits? Whether for added security or simple convenience, more features usually means better software. A well-rounded feature set takes a security solution from good to great. More than bells and whistles, added features provide security, usability and performance benefits.
UPDATES : Are timely updates delivered effectively? This rating is based on the frequency and versatility of virus database updates. Security software is only as good as its latest update. Viruses are being identified and added to signature databases all the time, so it’s important that your virus definition list updates accordingly. Modern antivirus software are equipped with automatic updates that perform regularly enough that you get faster updates that don’t slow down your system. The best security providers even “push” updates to you as soon as they’re available.
HELP & SUPPORT : Does the product offer additional support and helpful resources? This rating is based on the quantity and usefulness of additional product support. The best software doesn’t require reading an in-depth manual to use, but still has one available. For specific questions, troubleshooting, and additional help, the best antivirus manufacturers provide superior product support online and off. Additional support for software may come in the form of assistance over the 24x7 phone, email, live chat, or through a number of additional resources (knowledgebase, FAQs, tutorials).
BACKDOOR : A special type of trojan (often called remote access trojan or RAT), they essentially give control of your computer to a hacker.
THREAT DETECTION includes : Virus,Worm,Trojan,Spyware,Malware,Rootkit.
BROWSER EXPLOITS : malicious code that takes advantage of an internet browser vulnerability to make the browser do something you don't want (freeze, crash, change settings, etc.)
OS EXPLOITS : Malware that is designed to take advantage of a vulnerability in the Windows Operating System.
KEYLOGGERS : A virus designed to track and monitor user keystrokes, often used to steal passwords, credit card numbers, etc.
INBOUND EMAIL PROTECTION : The anti-virus software scans files received through incoming emails on a POP3 account.
OUTBOUND EMAIL PROTECTION : The software scans outbound email attachments so you don't spread viruses to others.
INSTANT MESSAGING PROTECTION : The anti-virus software scans files received through instant messaging (MSN Messenger, AIM, Yahoo Messenger).
P2P/FILE SHARING PROTECTION : The software protects from malicious files downloaded and/or accessed from peer-to-peer file sharing programs.
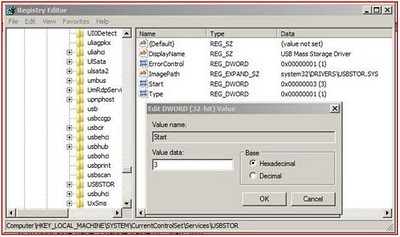
REGISTRY STARTUP PROTECTION : The software provides protection before the OS loads, or has the ability to scan registry files.
DIALERS : Malicious program that takes control of your computer and uses it to dial expensive phone numbers.
SUPPORTED CONFIGURATIONS : Does it incl compatibility with Windows 7 (32 bit),Windows 7 (64 bit),Windows Vista (32 bit),Windows Vista (64 bit),Windows XP (32 bit),Windows XP (64 bit)
 https://orcid.org/0000-0002-9097-2246
https://orcid.org/0000-0002-9097-2246