This post will focus on determining the IP addresses range from the target network. Here I will explore the tools needed to achieve it.
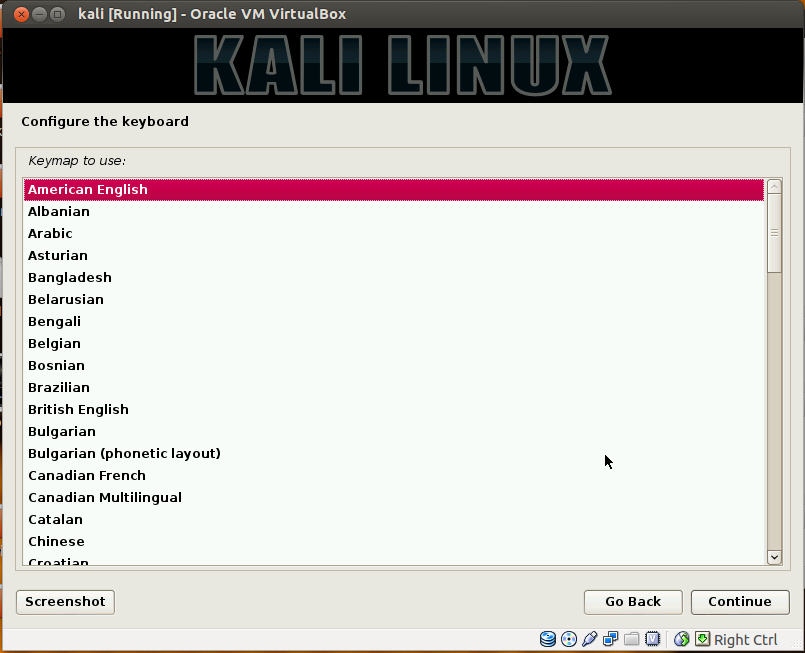
Let's begin the process of determining the network range by opening a terminal window:
1. DMitry
(Deepmagic Information Gathering Tool) is a UNIX/(GNU)Linux Command Line
Application coded in C language.DMitry has the ability to gather as much information as
possible about a host. Base functionality is able to gather possible
subdomains, email addresses, uptime information, tcp port scan, whois lookups,
and more. The information are gathered with following methods:
·
Perform an Internet Number whois lookup.
·
Retrieve possible uptime data, system and server
data.
·
Perform a SubDomain search on a target host.
·
Perform an E-Mail address search on a target
host.
·
Perform a TCP Portscan on the host target.
·
A Modular program allowing user specified
modules
2. Open a new terminal window and issue the following command:
dmitry -wnspb targethost.com -o /root/Desktop/dmitry-result
3. When finished, we should now have a text document on the desktop with filename dmitry-result.txt, filled with information gathered from the target:
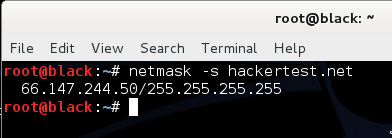
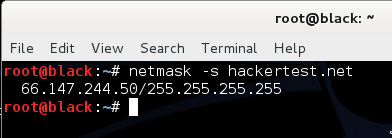
4. To issue an ICMP netmask request, type the following command:
netmask -s targethost.com
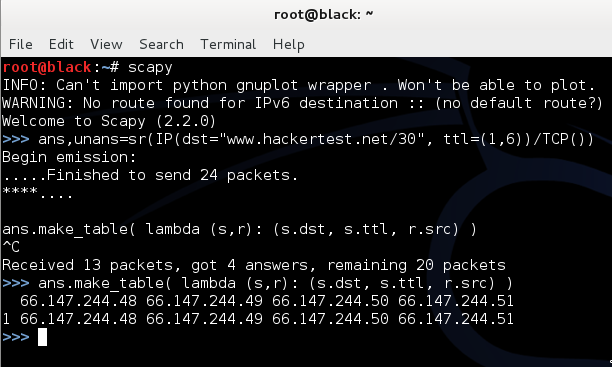
5. Using scapy, we can issue a multiparallel traceroute. To start it, type the
following command:
scapy

6. Scapy is a powerful interactive packet manipulation program. It is able to forge
or decode packets of a wide number of protocols, send them on the wire, capture them, match requests and
replies, and much more. It can easily handle most classical tasks like
scanning, tracerouting, probing, unit tests, attacks or network discovery (it can replace
hping, 85% of nmap, arpspoof, arp-sk, arping, tcpdump, tethereal, p0f, etc.).
It also performs
very well at a lot of other specific tasks that most other tools can't handle,
like sending invalid frames, injecting your own 802.11 frames,
combining technics (VLAN hopping+ARP cache poisoning, VOIP decoding on
WEP encrypted channel, ...), etc.Now with scapy started, we can now enter the following function:
ans,unans=sr(IP(dst="www.targethost.com/30", ttl=(1,6))/TCP())
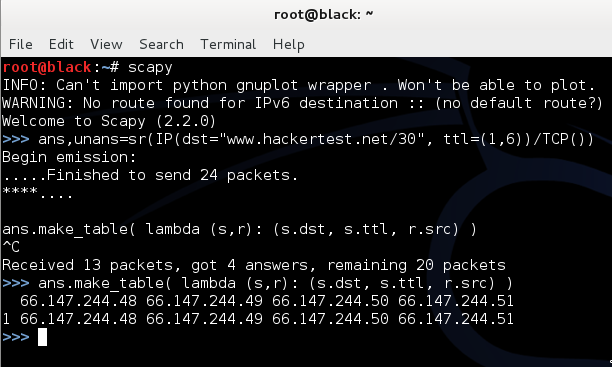
7. To exit scapy, type the following function:
exit()










 https://orcid.org/0000-0002-9097-2246
https://orcid.org/0000-0002-9097-2246