Saturday, December 03, 2011
Windows 8 Developer Pre BETA : How to get full screen on a VM?
Thursday, December 01, 2011
Windows 8 Developer Preview : Pre Beta Version for Developers
Wednesday, November 02, 2011
DUQU's MICROSOFT LINK!!!
Wednesday, April 27, 2011
HOW DO U FIND IF YOUR PC IS HACKED?- PART 6
HOW DO U FIND IF YOUR PC IS HACKED?- PART 5
HOW DO U FIND IF YOUR PC IS HACKED?- PART 4
HOW DO U FIND IF YOUR PC IS HACKED?- PART 3
HOW DO U FIND IF YOUR PC IS HACKED?- PART 2
HOW DO U FIND IF YOUR PC IS HACKED?- PART 1
Wednesday, March 02, 2011
ANDROID & GOOGLE : AT LOGGER HEADS????
Wednesday, February 16, 2011
NOKIA should have merged with GOOGLE : Google CEO
Tuesday, February 15, 2011
NOKIA & MICROSOFT : A MERGER TO READ ABOUT
Wednesday, February 09, 2011
MALWARE & AUTORUN : LOVE BIRDS OF PROPOGATION
Tuesday, November 02, 2010
MICROSOFT & Failures!!!
- February 2010 saw Microsoft announcing discontinuation of "Xbox Live service for original Xbox consoles and games.
- April 2010, Microsoft confirmed stopped working on tablet project, codenamed Courier which was touted to be an Apple iPad rival.
- September 2010, Microsoft announced that the Windows Live Spaces blogging service will be Terminate gradually in favour of WordPress.com.
- May 2010, Microsoft announced halt on the Response Point phone system.
- June 2010 saw Microsoft announcing discontinuation its new generation of smartphones.
- September 2010, Microsoft announced closure of Vine, a service built to help keep friends and family in touch during emergencies.
Tuesday, October 19, 2010
Service Packs & Infection Rates
Tuesday, October 12, 2010
Biggest release of Patch update by MICROSOFT
Wednesday, August 25, 2010
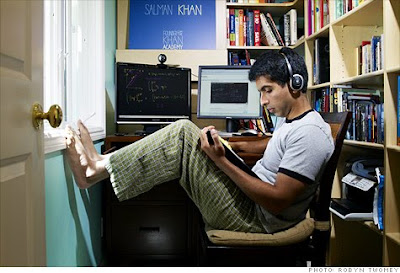
BILL GATES & Khan Academy
Sunday, March 07, 2010
Search Web by FACE recognition - Work is ON!!!: ONE ALBUM
Tuesday, January 19, 2010
Google vs Bing : On Data retention policy change

Monday, January 18, 2010
ZUNE 120 GB

Features
2. Main menu has the following scroll down as shown in screen shot from my ZUNE.
- Music
- Videos
- Pictures
- Social
- Radio
- Market Place
- Games
- Settings

3. Further brief on few of these of interest are enumerated below
Market Place allows browsing, previewing & downloading music directly from Microsoft's Zune Marketplace online store. Marketplace submenu further allows choosing between browsing Songs, Albums, and New Releases, or search for specific music by keying in a few letters. Songs can be previewed for 30 seconds with the option to add them to your virtual cart or purchase and download immediately. By signing up for Microsoft's Zune Pass music-subscription service (a free 14-day trial is available).....still to be availed by me.....
ZUNE is WiFi enabled and allows keying in the passwords if required vide Zunepad.
Radio : An interesting part of my first few days of interaction with ZUNE was non running of FM stations till the time I got link to this thread ie http://vasudevg.blogspot.com/2007/12/zune-fm-radio-tip.html that involved simply changing country from preset US to Europe
Video format : The only problem that I faced was that the horde of movies that I possess do not run directly on this.One needs to convert them to zune/ipod format with easy to use Windows Media Encoder....time consuming but worth it when we play it here on the ZUNE......I converted Sivaji Rajinikanth(...my fav) with a third party software Cucusoft...but was labelled with trial version watermark throughou(screen shot down)....rest was quiet ok....then converted with windows media encoder...and worked perfectly fine....gr8 output in video and sound....
Ports : Only two including one to ear phone and the other to USB for interface with PC for sync and charging battery.
Capacity : 120 GB...thats awesome for storage!!!!!
4. Any one across with any difficulty or query on Zune player can just leave his/her problem....will get back asap.......thats a promise for while.....

 https://orcid.org/0000-0002-9097-2246
https://orcid.org/0000-0002-9097-2246










